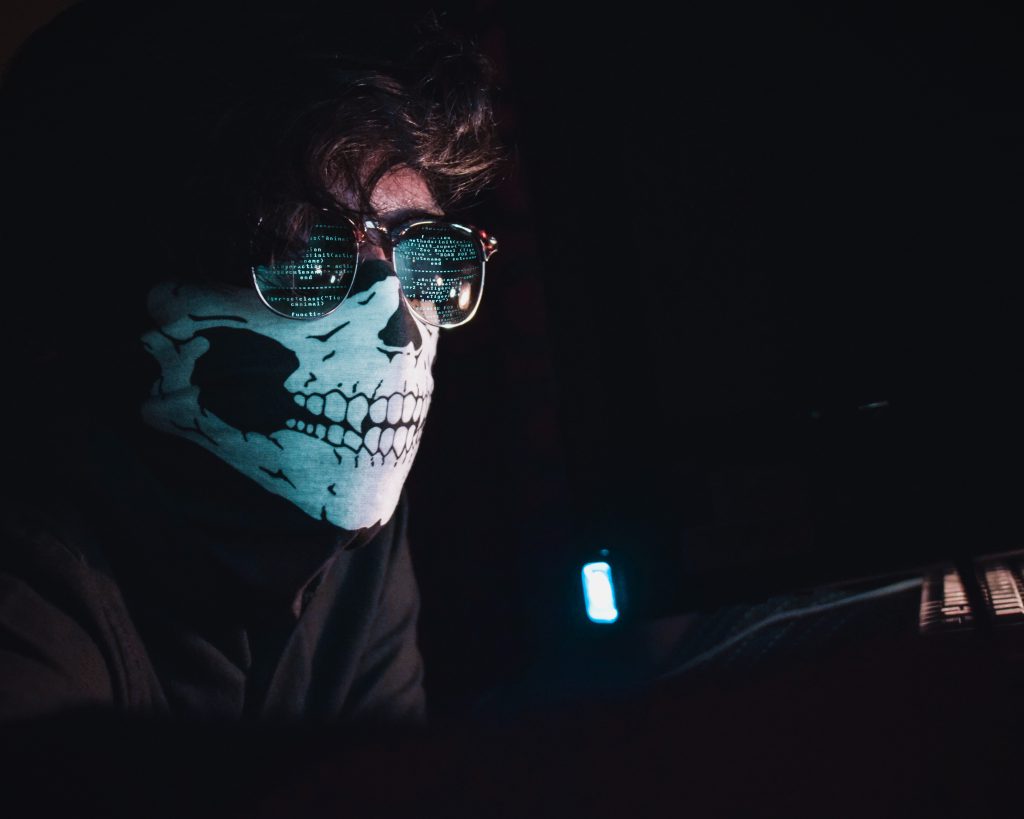
They are creeping around many corners in cyberspace − nefariously cloaked tricksters (bad actors, black hats, hactivists, script kiddies – pick one) who may be out for more than just pulling minor pranks. Just as parents rifle through their kids trick-or-treating haul to search for something dangerous or corrupt, so should cyber users be wary.
With October being National Cybersecurity Awareness Month, cybersecurity cadets Jared Johnson, Andrew Lindenmeyer, Robert Roser, Shiloh Smiles and Trey Stevens developed this list to help raise awareness about these ongoing threats. Lindenmeyer and Smiles are two of the college’s CyberCorps scholars, their junior and senior years funded with National Science Foundation grants that will lead them to cybersecurity-related positions with a federal agency after graduation.
- Deep Fakes
Deep fakes use Artificial Intelligence (A.I.) to piece together existing footage and sound clips in order to fabricate fake clips that are super realistic, to the point where many believe it to be true. A.I. has gotten to the point where, with enough audio samples, it can simulate your voice into saying sentences that’s not close to anything that you really said.
2. Social Engineering
Social engineering is the act of manipulating people to gain information and data. The deception could be carried out as a fake phone call, a fake social media request or even a person coming to your door representing a “company.”
3. Phishing
Phishing is a threat, usually over email or phone call, where a hacker pretends to be a legitimate institution or company and baits users into clicking on a nefarious link or entering data into a fake official-looking form.
4. Ransomware
Ransomware is a type of malware, generally downloaded through a malicious website or a through phishing email. The ransomware spreads rapidly on a computer, “encrypting” all its files—essentially translating them to an unreadable language. You then are forced to pay the hacker real money, often Bitcoin, in order to get your files decrypted and back to normal.
5. Physical Security
Physical Security is one that we all tend slack on as we think we are protected with a strong password on our computers. When leaving our devices, we need to lock them in order to prevent any unauthorized people from getting to it. While it does not seem realistic, a few seconds may be enough time for someone to run an automated program to setup remote access into your computer. These programs can sometimes exist on regular looking flash drives that people fall victim to. The majority of the time it is a USB someone finds on the ground or discarded somewhere. The finder is temped to look at it on their computer and, before you know it, it takes over. Make sure to avoid any unknown items and to enable security and location tracking in case your device disappears.
6. IoT Attacks
IoT stands for Internet of Things which has become a popular term in the recent years. This is a generic term that goes from the wireless smoke detector to the Amazon Alexa you have set up in the living room. Anything that is a device that connects to the Internet qualifies as an IoT device. Attacks on these devices are very bad when exploits are found. Depending on your IoT device, it may not receive updates as often as your computer and, since it is a smaller device, chances are the operating system is a stripped-down version compared to the full package. An IoT device may contain a stripped-down version in order to conserve space but this tends to cut out important security features. These devices should, instead, have stronger security because of the functions they can control. Enable every possible security option your device has, or research those that have the highest level of security.
7. Public Wi-Fi
The danger of public Wi-Fi is that nefarious people can often operate undetected. They can run tools called “packet sniffers” which essentially grab little “packets” of your data being transmitted. These packets could potentially include your credit card information or passwords. Additionally, people can trick you into joining networks and infect you with malware.
8. Data breaches
Data breaches are security breaks where massive amounts of data are leaked or stolen from a database, usually a company. This has multiple negative side effects. It hurts the company, which loses customers and credibility, the users who are now at risk due their personal data being in the hands of bad actors and it potentially hurts future users by giving hackers more credentials to try on other websites.
9. Credential Stuffing
Credential stuffing is a specific type of cyber-attack use hackers use. Essentially, they take a large bank of hacked username/password combos and try them very rapidly against a website. If one happens to pass, they gain access into a user account. People who reuse usernames and passwords are vulnerable to this.
10. Accidental Sharing
With corporate and personal email being the leading sources of accidental data leaks, it is easy to see why accidental breaches are a top risk when securing information. The main cause of this is ignorance: an estimated 60% of organizations have not educated their employees on securing information. By simply understanding what phishing emails are, or by keeping passwords secure, can decrease the chances of exploitation significantly.
Interested in studying cybersecurity?
The Citadel offers a Bachelor of Science in Cyber Operations. Those graduating with that degree will be able to:
- Apply security principles and practices to the design and implementation of the physical, software, and human component of the cyber systems
- Analyze and evaluate cyber systems with respect to security
- Identify, analyze and mitigate threats in the cyber systems
The Citadel is designated as a National Center of Academic Excellence in Cyber Defense Education by the National Security Agency and the Department of Homeland Security. Citadel cadets and students are eligible to apply for Department of Defense (DoD) Cybersecurity Scholarship (CySP) programs. The success rate for our students obtaining DoD CySP is 100%. And, The Citadel secured $2.8 million, establishing National Science Foundation CyberCorps Scholarship for Service (SFS) program in 2020, the first SFS Program in the State of South Carolina.
For more information please call (843) 953-1089 or email dhoward2@citadel.edu.

 The Citadel recognizes state and national leaders with honorary degrees
The Citadel recognizes state and national leaders with honorary degrees Awards presented to top cadets during 2026 commencement ceremony at The Citadel
Awards presented to top cadets during 2026 commencement ceremony at The Citadel The Citadel Class of 2026 cadets sworn in as officers in the United States Armed Forces
The Citadel Class of 2026 cadets sworn in as officers in the United States Armed Forces

